The largely invisible Northern Ireland/Republic of Ireland border area is subject to an enormous amount of mostly invisible electronic surveillance, some of which is worth detailing.
This post will look at the surveillance of people, of vehicles and then of goods and has been aided in some parts by conversations with persons formerly employed in intelligence services.
The important point to note is that the notion of ‘border’ is now obselete – the territories adjacent to borders are so subject to overwhelming electronic surveillance that ‘border’ is everywhere.
Surveilling People – the mobile phone
While electronic ankle-tags still exist, whether using radio frequency or more modern GPS technology, they have been largely superseded by the citizen’s voluntary sporting of a much more sophisticated tag – the personal mobile phone.

Since everyone’s mobile phone is directly linked to a contract with a telecoms’ provider detailing the user’s name, address, telephone number and associated banking details – both those companies and governments have a method of tracking the location, journeys and activities of all phone-bearing citizens at all times, night and day whether at home or travelling.
And since some telecoms providers are multinational entities spanning many borders, a single mobile phone company may have data on its computer servers relating to many millions of citizens of many different nations making its servers a target of hackers of both the criminal kind and of the kind bent on preventing crime and terrorism.

Whether the mobile phone is stationary or mobile, its movements are minutely tracked by ubiquitous cell towers that enable connectivity – while the telecoms companies are tracking your phone for service and billing reasons, other agencies are using that information to enable ‘real time’ tracking of all phone users.

Mobile phone customers communicate their positions with their networks of cells every time they use their mobile phones to text or make a call and through ad-hoc events generated when changing local area code (LAC) or through applications running on smart phone devices, such as web searching, location services etc.
Each such communication is registered by one of the network cells as an ‘event’ with a unique and anonymous user ID, a timestamp, a local area code (LAC) and the cell’s ID being attributed to it.
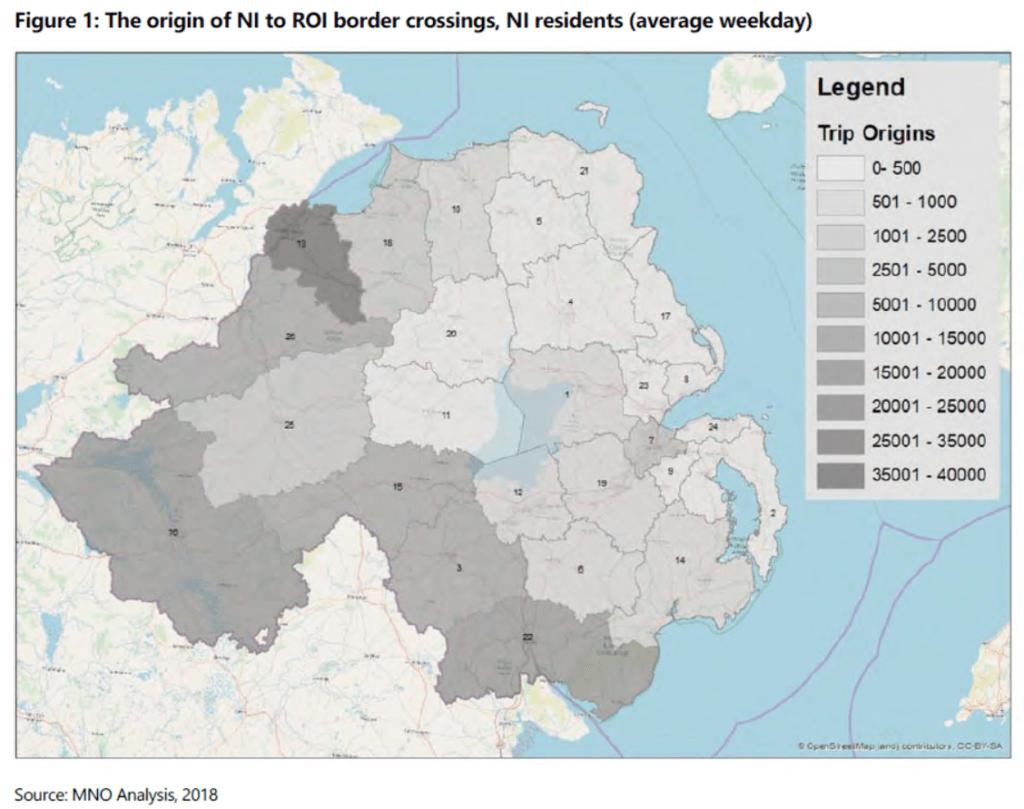
One example of the tracking of people crossing the Northern Ireland/Republic of Ireland invisible border is shown in the study commissioned by the Northern Ireland Department for the Economy (DfE) that used mobile phone data to analyse border crossings (both ways) by persons, including their starting points and destinations whether those were in Northern Ireland or the Republic of Ireland.
The gigantic tranche of mobile phone data (“billions of events”) was ‘aggregated’ and ‘anonymised’ before being given to a private company – Citi Logik – with the result that the study was able to track the behaviour of travelers crossing the [invisible] border, both ways, detailing starting points, journeys, destinations and ‘dwell times’ on the way to and from…

Before the data set was ‘anonymised’, it contained all of the personal data of each and every one of the mobile phone users – their names, addresses, bank account payment details, travel times, stopping points (if any), destinations, time spent at destinations, not forgetting their return journeys in their entirety – not forgetting all the numbers (persons) they called.
Retention and sale of Mobile Network Data has become an unexpected profitable source of income to mobile telecoms companies.
The use of anonymised mobile network data (MND) to understand mobility patterns has become increasingly popular. In just five years, it has become the ubiquitous data set in transport and urban planning.
Traditional survey methods are expensive, potentially disruptive, prone to human error and provide only a limited snapshot in time.
MND is considerably more cost-effective and can provide information on population and vehicle flows both historically or in real-time.
MND has a valuable role as an integral data source providing insights to better inform decision making in the development of transport and urban planning models.
MND has a huge amount of untapped potential. Many people have never heard of it or seen it in action.
In the future, it could be applied to a far broader range of sectors, as well as being combined with emerging technologies such as the Internet of Things.
https://www.citilogik.com/mobile-network-data
The report by Citi Logik was the first occasion that authorities in Northern Ireland admitted authorising the transfer of British and Irish citizens’ mobile phone tracking data from a private commercial telecoms provider to a private commercial data-mining company.
While Citi Logik also offers ‘real time‘ data analysis services, its report for DfE used what is described as ‘historical‘ data – data a few days or week old.
It is only referenced here to indicate the scale of citizen-tracking both ways across the invisible border between Northern Ireland and the Republic of Ireland.
The security services – unlike authorised private commercial companies – have “real time” access to ALL commercial mobile phone data that enables tracking of individuals and also of ‘aggregated’ targets – crowds of whatever size.
In fact, security services with access to all commercial mobile phone data (accessed from and analysed in locations such as GCHQ) can track all phone-owning citizens round the clock, while analysis of ‘historical’ data enables investigation of recent crimes and acts of terrorism.
Pegasus Spyware
Pegasus software has been in the news for a few years – it is an Israeli mobile phone ‘spyware’ that can be remotely and secretly installed on any mobile phone – it has been involved in political scandals across Europe, from Hungary to Poland and Spain.

Produced by Israeli security company NSO, it is normally only sold to governments or to government agencies – while critics claim that it is only sold to repressive governments or political parties in government with repressive tendencies.
When Catalan independence politicians recently claimed their mobile phones were infected by Pegasus spyware allegedly by the Spanish Socialist government, it turned out that the phones of both the Catalans AND the Spanish Socialists were ALL infected.
The committee’s initial session in April, to deal with preparatory work, coincided with revelations about the so-called CatalanGate, an investigation into espionage of separatist leaders with ties to Catalonia’s failed unilateral breakaway attempt from Spain in 2017.
And its next session will take place right after Spain’s prime minister, Pedro Sánchez, on Monday said that his own phone was hacked by Pegasus.
Other senior members of the Spanish government have apparently been targeted by the spyware, including Defense Minister Margarita Robles and former foreign minister Arancha González-Laya, whose cellphone communications were spied on during a diplomatic crisis between Spain and Morocco in May 2021, government sources said.
Spain’s leading newspaper – El Pais – covered the story here.
One unexpected result of the Spanish Pegasus scandal was the dismissal of Spain’s Intelligence chief.

The primary advantage of software such as Pegasus (one of many such products) is that it enables governments – those that don’t have the scale of Britain’s GCHQ facility or America’s NSA facilities – to spy on individuals, journalists, activists and citizens DIRECTLY without having to harvest ‘real time’ MND from mobile phone providers.
Software products such as Pegasus can be secretly and remotely installed on any user’s phone, turning it into an ‘always on’ recording device, providing audio and video recording via the phone’s own microphone and camera(s), while also giving full access to all of the App data on the phone – passwords, emails, texts, sms messages and so on.
The US government banned the import and use of Pegasus, depriving the company of its most lucrative customer base: US law enforcement agencies.
Apple added to the pressure, suing the company, and alerting owners of infected iPhones. That put the company under extreme financial pressure, which may see it disappear – or may just make things worse.
Screenshots came to light as a result of investigative journalism by the financial publication Calcalist into potentially illegal use of Pegasus by police within Israel. They show:
Activating the phone’s microphone to listen in live to the owner and anyone with them
https://9to5mac.com/2022/08/05/pegasus-screenshots/
Activating the phone’s camera to take snapshots of the surroundings
Listening to captured recordings of incoming & outgoing phone calls
Reading text messages
Reading WhatsApp messages

Pegasus-like software is only referenced here to highlight that a mobile phone is one of the best methods of tracking not only individuals but of masses of individuals, into the millions.
The Northern Ireland/Republic of Ireland border area has for many years been surveilled using MND and everyone who has ever crossed the invisible border in either direction has been recorded doing so.
What if mobile phones are switched off?
[A small disclaimer – the author studied a H.Dip in Computer Science at UCD and later a Masters in Computing in DIT, while in between working as a consultant for a large Scandinavian mobile telecoms organisation.]
There are different definitions of ‘off‘ in technology.
You may already be familiar with switching your computer or laptop to ‘sleep’ mode, or even your television to a form of ‘off’ that enables a faster start up later.
Even if you think your laptop or computer is ‘off’, your device contains a CMOS button battery that enables the ‘off’ device to continue to power chips that retain Basic Input/Output System data.

Sticking with mobile phones – phones may give the appearance of being ‘off’ [screen blacked out] but may still be communicating with cell towers and/or WiFi networks and/or Bluetooth devices.

Individual citizens may try to use this type of low power or ‘off’ state to track their own lost or stolen mobile devices.
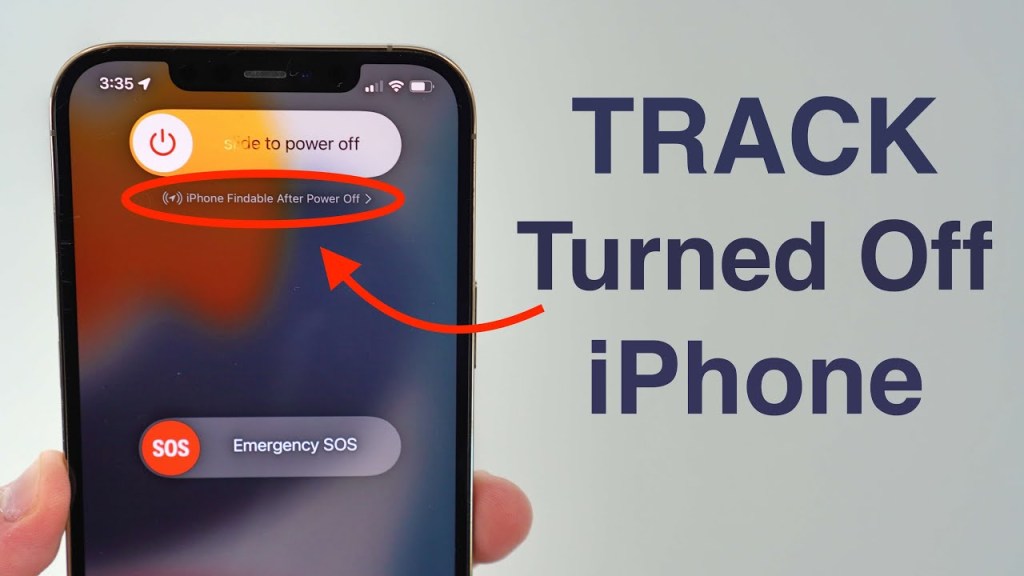
Be aware that governments and many commercial spyware companies may routinely track mobile phones that give the appearance of being ‘off’ when they are in fact still ON to different degrees, routinely accessing all of the Apps on the phones along with the microphones and cameras.
Surveilling People Who Don’t Carry Mobile Phones?
How to surveil if persons crossing the Northern Ireland/Republic of Ireland border purposely don’t carry mobile phones?
First of all, reference to a specific ‘hard border’ is far from the reality.
A border is a distributed concept nowadays composed of the mobile phone, road, rail and air networks on either side of what is termed a ‘border’ – not forgetting the maritime tracking of ports and shipping.

With the expansion of Internet connectivity into every aspect of society, information gathering and tracking of persons and things has become more sophisticated, more widespread and yet more covert.
Security checks have largely dispersed from what used to be known as ‘border checkpoints’ into society generally – in the form of ubiquitous traffic cameras, Automatic Number Plate Recognition cameras, speed cameras, toll cameras, underground and overground parking cameras, always-on Web cameras broadcasting across the Internet, CCTV security cameras and even DashCams and mobile phone cameras when these latter are used by the public and broadcast on social media.
Intelligence services have never had it so good – the public at large throw terabytes of data at them in the form of text, photos, videos and ‘real time’ streamed live video feeds – members of the unsuspecting public broadcasting live video of incidents in public and private spaces have been feeding prime Intel right into GCHQ and into various United States NSA facilities apparently unaware and uncaring that they are enabling surveillance of themselves and of those dear to them.
And so it is to the surveillance of road vehicles of all kinds that we now turn.
Surveilling Vehicles – Traffic Cameras and Traffic Counters
Roads on both sides of the invisible Northern Ireland/Republic of Ireland border are surveilled by a plethora of always-on traffic cameras which are photographing and video recording to and from the invisible border.

These cameras may be connected to computer systems operating Automatic Number Plate Recognition (ANPR) software offering the possibility to track and record vehicles along with the personal data of their registered owners.
Road traffic cameras are always becoming more sophisticated in terms of their technology and also by means of their connection to servers operating artificial intelligence which means that the data analysis occurs faster enabling ‘real time’ tracking of individuals.
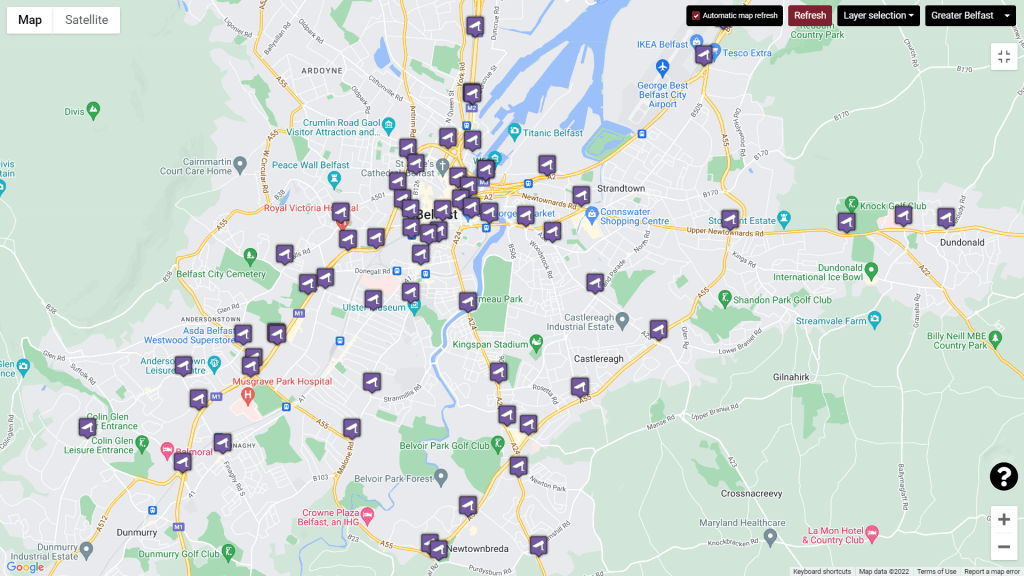
Traffic cameras proliferate around the Greater Belfast area, but are located at strategic roads approaching the invisible border.
More importantly, all vehicular traffic arriving at ports in Britain that might travel on ferries to Northern Ireland or to the Republic of Ireland has already been scanned and monitored on roads leading to the ferry ports and also then during the embarcation process in the ferry ports – so later scanning at ports in Northern Ireland or the Republic of Ireland represents a degree of overkill.
Locations of all fixed and mobile traffic cameras in Northern Ireland (including ‘red light’ cameras) may be read here.
There are 90 permanently signed locations where eight safety camera vehicles operate.
There are three fixed speed cameras, six fixed red light running cameras and three average speed enforcement cameras.
There are 234 active sites, 109 of which are permanent.
While local authorities may install and operate these overt cameras for reasons relating to traffic management and road safety, the security services may be interested to record and monitor these for other reasons relating to national security and prevention of terrorism.
It is reasonable to expect that there are very many covert cameras operating in areas of interest to the security services.
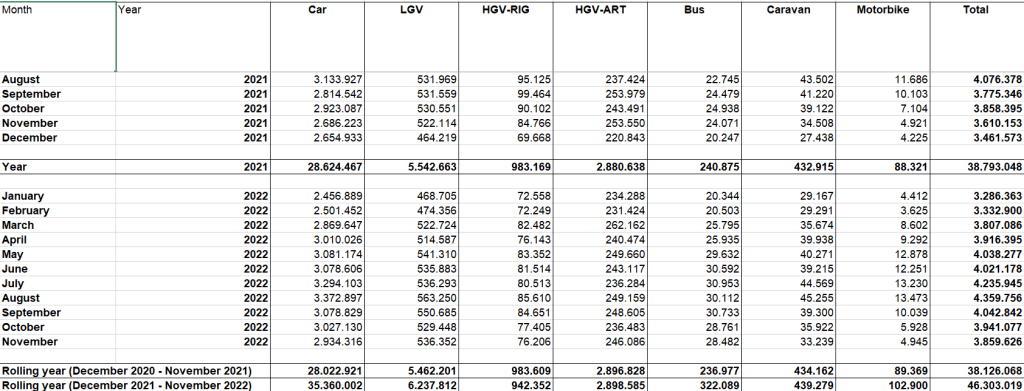
Apart from cameras, there are also ‘traffic counters’ at 15 border locations – devices which not only count vehicles, but also distinguish between their types in ‘real time’. (See here.)
Traffic counters may also be ‘tweaked’ to record other types of information, such as the passage of electronic toll tags.
In contrast to Northern Ireland, the Republic of Ireland has SCORES of traffic counters throughout the country.
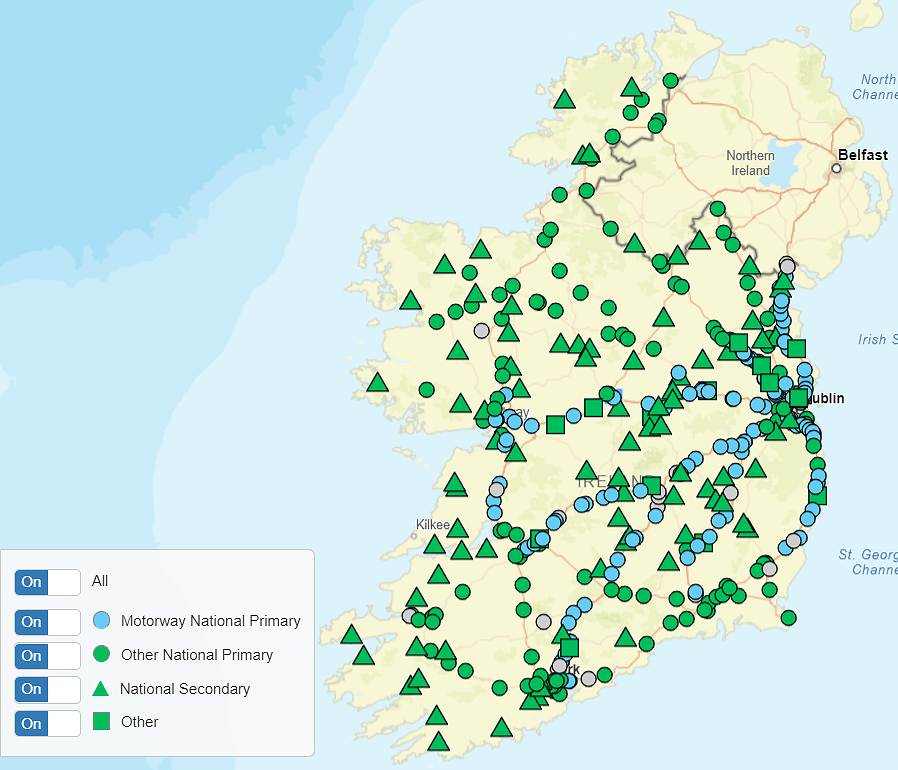
There are different types of ‘traffic counter’, above and below ground – but the majority of those used in the Republic of Ireland are of the inductive loop variety – buried under the road surface and invisible to the road user.
Traffic counters provide information on the volume of traffic by hour of day and vehicle class, i.e., motorcycle, car, goods vehicles distinguished by number of axles etc. with up to twelve vehicle classes being identified.
Vehicles are detected by passing over loops embedded in the road surface. It is possible from the data collected to establish the vehicle profiles and the various vehicle classes involved.
https://www.tii.ie/roads-tolling/operations-and-maintenance/traffic-count-data/
The ability to use ‘traffic counters’ to track – in real time – the passage of specific vehicle types along rural roads may be correlated with other traffic camera (photographic and video) data to pinpoint vehicles that are endeavouring to avoid toll booth checkpoints.

Almost everyone is familiar with the large, blunt, in-your-face toll road checkpoints in the Republic of Ireland, particularly the toll on the M1 between Belfast and Dublin at Gormanston/Monasterboice.
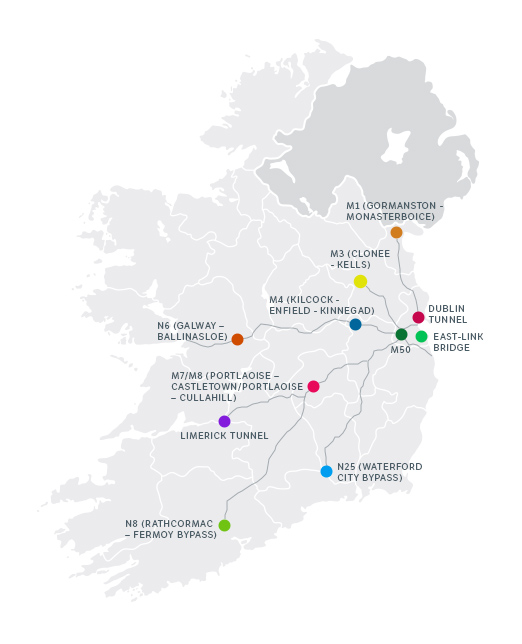
The major toll roads create and record a huge amount of ‘real time’ data on ALL vehicles passing through them – passenger vehicles, goods vehicles, buses, trucks, emergency vehicles – using a combination of ANPR (automatic number plate recognition), vehicle photographs including of front seat passengers, video recording and – because of the concentration of vehicles at that location – MND – mobile network data at adjacent cell phone towers.
In the April 1991 ‘Murder of a Rockstar’ television drama, Lieutenant Columbo solved a murder by accessing a speed trap photograph clearly showing a car driver attempting in vain to fool the camera using a paper photograph held in front of his face.

You don’t need Columbo to convince you that the technology photographing car drivers and passengers has greatly improved over the past 22 years.
An island surrounded by sea has a limited number of registered vehicles which are constantly monitored by a multiplicity of cameras and counters.
The only vehicular traffic capable of being added to the island number is that which mainly arrives by sea – and all of that vehicular traffic has been registered, recorded and checked before beginning any sea voyage to either Northern Ireland or the Republic of Ireland.
All of the data on vehicular traffic moving by ferry is already shared by security services.
As the sophistication of technology constantly increases, so too does national and international surveillance increase well beyond demarcation lines previously called ‘borders’.
There isn’t currently a vehicle moving around the roads of the United Kingdom or the Republic of Ireland that isn’t subject to electronic surveillance and that hasn’t already been surveilled.
Schengen Shenanigans Ireland
The Schengen Area is an area of European countries where inter-country travel is borderless or free of ‘hard border’ checks.
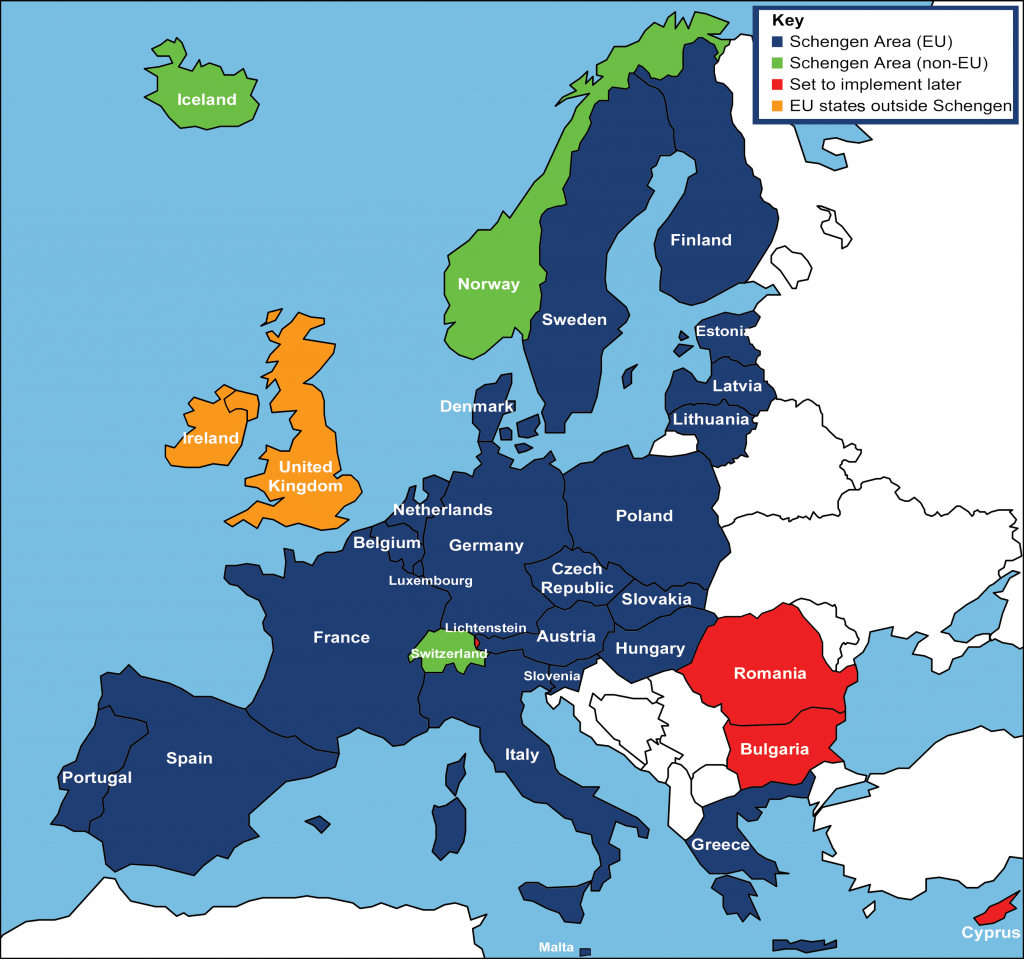
In the 1980s, Ireland partnered the United Kingdom in refusing to join Schengen, preferring to keep a ‘hard border’ for European citizens arriving at Irish airports or seaports while preserving the Common Travel Area with the United Kingdom.
As Ireland is not a party to the Schengen Agreement, Irish citizens must present a passport when entering other EU Member States.
Similarly, all EU citizens entering Ireland are required to present a passport or a valid national identity card.
Even Irish citizens returning to Ireland from European destinations – whose details have been screened at check-in desks at European airports fully visible online to Interpol and to remote Irish security authorities – are still required to present a passport on their return to Ireland.
The European Border Surveillance System (EUROSUR) is used by Schengen member states (and Romania, Bulgaria and Croatia) to co-ordinate and exchange information. It aims to stop cross-border crime.
Hot pursuit
Under the Schengen Agreement, police who are in active pursuit of a criminal can continue their pursuit into a neighbouring country provided that country is also in the Schengen Area.
Schengen Information System (SIS)
EU member states use the Schengen Information System (SIS) to share information about security and border management. Countries can issue a SIS alert about a person or object, which also includes information about what to do if that person or object has been found.
Ireland is connected to SIS II, which is the second generation of the Schengen Information System. This means that Ireland can send and receive alerts on people and objects. These alerts are used to help trace missing people, people who are wanted by the police in a member state, and/or objects that are missing or stolen.
With the sharing of ‘real time’ information across Europe and also with British security authorities, you have to wonder why Ireland imposes checks on its own and other EU citizens arriving on scheduled flights from EU airports.

The Department of Justice and Equality, which operates immigration at Dublin Airport via the Irish Naturalisation and Immigration Service (INIS), has installed new electronic passport machines in T1 and T2.
The self-service machines use automatic facial recognition and passport reading technology to conduct immigration checks on people arriving into the airport.
There will be 10 automatic passport control gates in T1 and 10 gates in T2. A Department of Justice and Equality spokesman said extra machines may be installed at the airport if it “makes operational and financial sense to do so”.
https://www.facebook.com/dublinairport/photos/a.517023948343972/1637115339668155/?type=3
Neither Irish citizens nor Irish political leaders threatened acts of terrorism (by themselves or by other groupings) at the retention of these ‘hard border’ controls which are largely obsolete since all travelers by air and sea to and from Irish airports (and ferry ports) are identified and recorded prior to travel anway, whether in Ireland or in their originating European mainland country and their information is subject to checks and scrutiny by both Irish and European security authorities before they get on the aircraft.
As at Dublin airport’s ‘self-service machines’ where ‘automatic facial recognition and passport reading technology’ is installed and working, the future of travel and identity checking is becoming automated based on software, artificial intelligence and biometrics.

In fact, Ireland has chosen to police the UK/Ireland Common Travel Area at Irish airports and ports by refusing entry to persons regarded – by Irish authorities – as unlikely to fulfil UK immigration rules.
Since EU member country Ireland relies on the non-EU United Kingdom for defence of its airspace, for defence of its far off maritime borders and for defence of its undersea assets – highly valuable Internet cabling and electicity connectors – returning the favour of policing UK borders at Irish airports and seaports is the LEAST Ireland can do.
The physical infrastructure of so-called ‘hard borders’ within the Schengen area has disappeared but has been replaced by the electronic surveillance described above.
Individual European countries still monitor and record border traffic for a multitude of reasons – reporting congestion, warning of weather events on particular roads, road safety and maintenance, forest fire dangers, landslides, including estimates of business and tourist traffic – all of this information is necessary for future planning of infrastructure.
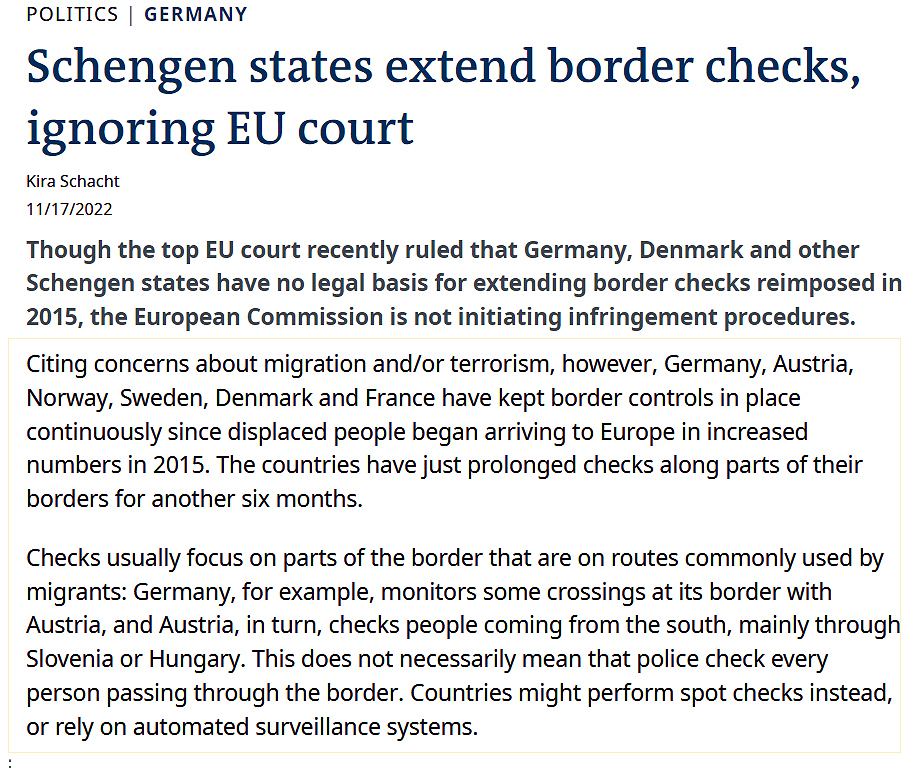
And individual European countries have re-introduced ‘hard border’ controls whenever they felt it was necessary to do so, matters the European Court has decided to ignore for some years.
FRONTEX and Biometrics
FRONTEX is the European Union’s border control agency and it is expanding its reach and capabilities, especially in relation to automated border controls using technology, artificial intelligence and biometrics.
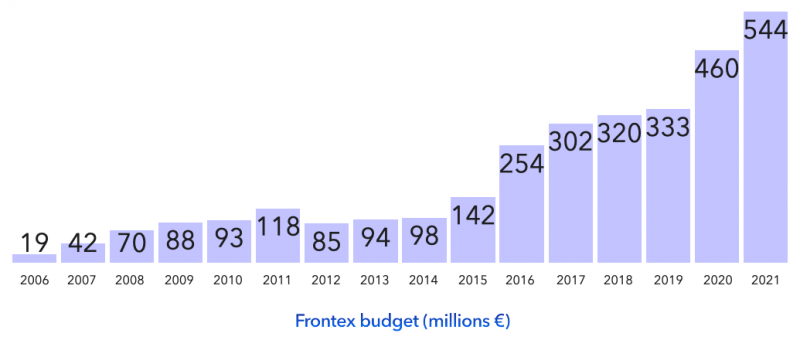
It is the rise in migrant entries to the EU that has fuelled the expansion of FRONTEX.

In tests at Spain’s border with Gibraltar and Bulgaria’s border with Turkey, FRONTEX installed and tested its automated biometric Entry Exit System (EES).
Frontex has just completed the Entry Exit System pilot project at land borders, which was hosted by Spain and Bulgaria. The exercise simulated the future EES environment by collecting and cross-checking the required data in full compliance with fundamental rights and personal data protection measures. During the trial, four travellers could be processed at the same time under the supervision of one border guard, proving the efficiency of the system while maintaining direct control of law enforcement officers.
As part of the trial, practical demonstrations of the systems took place at Bulgaria’s border with Turkey and Spain’s border with the UK (Gibraltar) and included self-service kiosks, seamless corridors and mobile devices used for registration and verification of travellers.
Participants observed the processing of passengers and received feedback from colleagues operating the system. The lessons learned and practical operational outcomes will be used by Member States’ border authorities and European agencies alike as the EU prepares for the implementation of the EES.
https://digit.site36.net/2021/11/09/new-control-system-frontex-ends-pilot-project-on-facial-recognition-at-eu-borders/
The EES referred to here is for EU borders that face into non-EU territories and where travelers’ biometric data is captured for the first time only.
With its coastguards and border guards, this is the European Union institution that has expanded the most rapidly. In the space of 15 years, Frontex has become the key agency in Europe’s migration policy, ensuring control of the periphery the Schengen Area and policing the Mediterranean, from its headquarters in Poland down to Spain and the south of Albania.
But its detractors condemn this as a further manifestation of “Fortress Europe”.
https://www.etui.org/sites/default/files/Hesamag_20_EN_32-36.pdf
Travelers originating in Ireland or the UK have biometric data that originated in and was first captured and processed in these territories – when they applied for national insurance or social security numbers, drivers’ licences, passports, vehicle registrations – and where they supplied the authorities with photographs of themselves – checks on citizens of these territories are made much easier because their data has been recorded over many years and has provable provenance.
These are all citizens of an area currently (and previously) designated as the Common Travel Area.
It would be difficult for the EU to argue that electronic/online checking of biometric data of UK citizens would need ‘hard border’ controls such as those described in exaggerated fashion by Ireland’s Leo Varadkar.
For many Human Rights’ activists, the expansion of FRONTEX has very negative implications:
Lobbying Fortress Europe – The making of a border-industrial complex
MILITARISATION
The massive expansion of the budget, personnel, and powers of the EU’s border agency Frontex has also seen increasingly privileged access for industry.This perpetuates a vision of border control based on more and more firearms and biometric surveillance that has major human rights implications.
https://corporateeurope.org/en/lobbying-fortress-europe
Ireland has recently begun funding FRONTEX and attending FRONTEX meetings for the first time.

FRONTEX will eventually want to take its rightful place in securing the EU’s far off Ireland/UK border if political considerations do not intervene.
Surveilling Goods in Transit
All borders in previous times condoned a degree of smuggling – whether because minute surveillance was beyond the ability of authorities back in the day or because it might have been in their interests, but those days are gone.

Irish governments allowed a great deal of IRA terrorism to cross the actual border into Northern Ireland or, if you prefer, ‘did not strive Officiously’ to prevent a great deal of IRA terrorism occuring around and across the Northern Ireland border.

The Provisional IRA’ Chief of Staff Thomas ‘Slab’ Murphy’s cross border smuggling empire lasted for years untouched and was only confronted by authorities long after his and the IRA’s fortune had been made and laundered – according to Brian Feeney and The Irish Times.

Weapons and ammunition could be quite small and easy to conceal, but tons of explosives in the form of trucks of prepared nitrogen fertilizer bombs and/or vehicles carrying Jim Monaghan’s IRA mortars tubes and warheads – all of these were regularly prepared in the territory of the Republic of Ireland and had little or no difficulty in crossing areas of the totally unserveilled border, courtesy of nationalistic/republican Irish government inaction.

But now the notion that anything such as a tomato or a potato or a carrot might be smuggled into the Republic of Ireland from Britain via Northern Ireland is to be taken seriously – so let’s take a look at surveillance of goods.
We are only concerned here with goods arriving in Northern Ireland – goods that largely only arrive by ferry from what is termed the UK mainland and mainly in sealed CONTAINERS aboard registered lorries/trucks and usually originated by and transported by registered businesses with a proven track record.
From the point of view of British authorities, they are already managing a gigantic surveillance operation of roads, ferries and ferry ports, lorries/trucks and containers before these goods intended for Northern Ireland ever reach the embarcation stage.
Tracking Containers
The era of the ‘Secure Cross Border Transport Model‘ dawned some time ago, and could more simply be termed the ‘Smart Tracking of Road Freight‘ [or Containers] – in fact, the tracking may be applied to air and sea freight as well.
Developments in information and communication technologies (ICT), satellite positioning systems (SPSs), cellular communication systems (CCS), radio frequency identification (RFID) technology, geographical information systems (GIS) and advances in web based software with visual graphics and other user friendly features, offer a tremendous potential to deal with major challenges in cross-border transport.
Combined use of these technologies can secure and track vehicles and goods in real time, thereby allowing control authorities to take timely action.
Not only are the trucks or lorries connected and tracked by both GPS and cellular devices, but also the individual containers are themselves tracked as are their electronic seals.
[here]

In fact, the technology available to monitor individual containers can record every movement even down to the degree of tilting that the container is undergoing.
The lock seals attached to the containers are SMART – in fact they are in effect metallic mobile phones that constantly talk to their far off controllers.
Since 2006, all new goods and passenger vehicles driving in EU territories MUST have a Digital Tachograph installed and these are VERY SMART indeed.

Tachographs are fitted in both passenger and goods’ vehicles that fit within the tachograph ruling.
As of 2006, it became a legal requirement to have a digital tachograph installed on your new vehicle (within the categories of passenger, commercial and goods).
The more advanced version of its well-known predecessor, the analogue tachograph, the digital tachograph records information on a range of vehicle and driver activities, including:
- Driver activity: This includes what the driver is doing (e.g. driving, working or having a break).
- Distance travelled by the driver
- Date: logged across all activity to ensure the correct hours are assigned to the correct dates.
- Date and time of each individual activity, including changes made by fleet managers and/or drivers.
- Tachograph calibrations: This needs to be inspected by an Approved Tachograph Centre every two years to ensure correct readings are recorded.
- Events that take place, like Card Inserted whilst driving, as well as any faults that happen during the journey.
- Vehicle speed: This is recorded for every second of movement.
- Enforcement checks made by either management or the emergency services like DVSA.
- Any tampering with the system: With digital tachographs, this is nearly impossible to do and, in the vast majority of cases, any tampering activity will be captured.
- The number of times a driver card is inserted each day: This may include moving from one vehicle to another, or could be an indication of tampering.
- Whether there was a single or two co-drivers: In this instance, there may be co-drivers as a result of the laws that were introduced in 2007, regulated by the EU. The non-stop driving time may not exceed 4.5 hours for a single driver, after which time, the driver must take a break. However, if you are sharing the driving with another individual, this enables a crew’s duties to be spread over a longer period of time.
- Vehicle registration number.
The daily driving allowance for any single driver is a maximum of nine hours, with a minimum of a 45 minute break per 4 and a half hours of driving. This daily driving limit can be increased to 10 hours, only twice per week with the appropriate breaks also taken. There is a weekly driving limit of 56 hours, which applies to a fixed week and must include at least one weekly rest; a fixed week starts at 00:00 Monday and ends at 24:00 the following Sunday.
These rules have been put in place by the EU and must be upheld when driving through any European Union country, with any checks to be made prior to entering the country to allow for extra restrictions.
https://www.optac.info/uk/tachographs/
Not only are the trucks and containers trackable at all times on land, they are also trackable at sea.

Individual containers may carry SMART e-lock seals capable of using different methods of contacting Base Controllers and since they are BROADCASTING events in their journeys, not only may the Controllers listen to them in ‘real time’, but also security services may also eavesdrop on their broadcasts where necessary.
The short version of the entire blog post preceding this sentence might be summarised as: Everywhere is Border.

Since the very fabric of our societies – whether on land, on the seas or in the air – is subject to sophisticated surveillance, monitoring and recording of people and goods to an extreme degree only dreamed of by writers of a recent time, how honest was it of Leo Varadkar (and his unmerry Pan-Nationalist Grim Choir) to describe a modern, SMART “border” as follows:
As I edge toward 1,000,000 readers of my blog, I want to thank all of you for reading this far.


Interesting article. The border further walks into irrelevancy when they role out the remote scanning of individual items not just containers. In the next few years we will not even have to stop at a checkout in a supermarket, we will simply push our trolley’s through and they will be automatically tallied up and debited against your bank account via RFID technology or lazar recognition. This will be easy to role out along roads too thereby eliminating any need for a physical border.
LikeLike
Did you spot the whopper by Mary Lou McDonald there? ” All of us built the GFA”.
She joined Fianna Fail in 1998 when it was signed!
LikeLike